We have been told for years that our passwords for emails, online banking, shopping etc. need to be long, contain capitals, numbers, and special characters. These can be a nightmare to remember, and many people end up using the same one for everything or just replacing letters with special characters. Such as C0mput3r or some other word that is recognisable. … Read More
Email Security and the Microsoft Exchange Vulnerability
Email security is the hottest topic in Cyber right now. Mainstream news channels are extensively reporting on the newly publicised vulnerability in Microsoft Exchange. What is a vulnerability in software? This is usually a weakness, glitch or flaw present in the code of the software. Without fixing these, vulnerabilities can impact the performance and security of the software. These glitches … Read More
Phishing Emails and Office 365
What are phishing emails? Phishing emails are sent to trick you into divulging a password of some kind or other personal details. Some estimates claim the number of fake emails sent each day is now in the billions. During these long periods of working from home due to Covid, many workers are unable to quickly ask a colleague if they … Read More
Criminals Are Using Coronavirus in New Email Phishing Scams
Since the World Health Organisation (WHO) declared the Coronavirus as an international emergency at the end of January, cybercriminals have predictably encorporated it into their last scams. They have been sending out emails proporting to be from the Center for Disease Control and Prevention and the (fictional) Wuhan Medical authorities. These emails contain a link that will show an updated … Read More
Microsoft Office 2010 End of Life is October 2020
Office 2010 has now been around for 10 years but in October of this year Microsoft will stop supporting the software and no longer release security updates. As with Windows 7 and Server 2008 at the end of 2019 this means the software will be vulnerable to attacks through malicious code. What are the options for upgrading? Microsoft has released … Read More
Windows Server 2008 End of Life – Is Your Business Ready?
Windows Server 2008 end of life is happening on January 14th 2020 – this means Microsoft is stopping all official support for the operating system. There will be no further security updates for servers running it and they could be vulnerable to attack from outside sources. The operating system was first launched February 2008, so it has had a good … Read More
Windows 7 End of Life is January 2020 – is Your Business Ready?
When Microsoft released its popular personal computer operating system, Windows 7 on October 22, 2009 it pledged to give users 10 years of support. Those 10 years are now up and the company is stopping support for Windows 7 on January 14th 2020. What does end of life mean for Windows 7? End of life simply means that Microsoft no … Read More
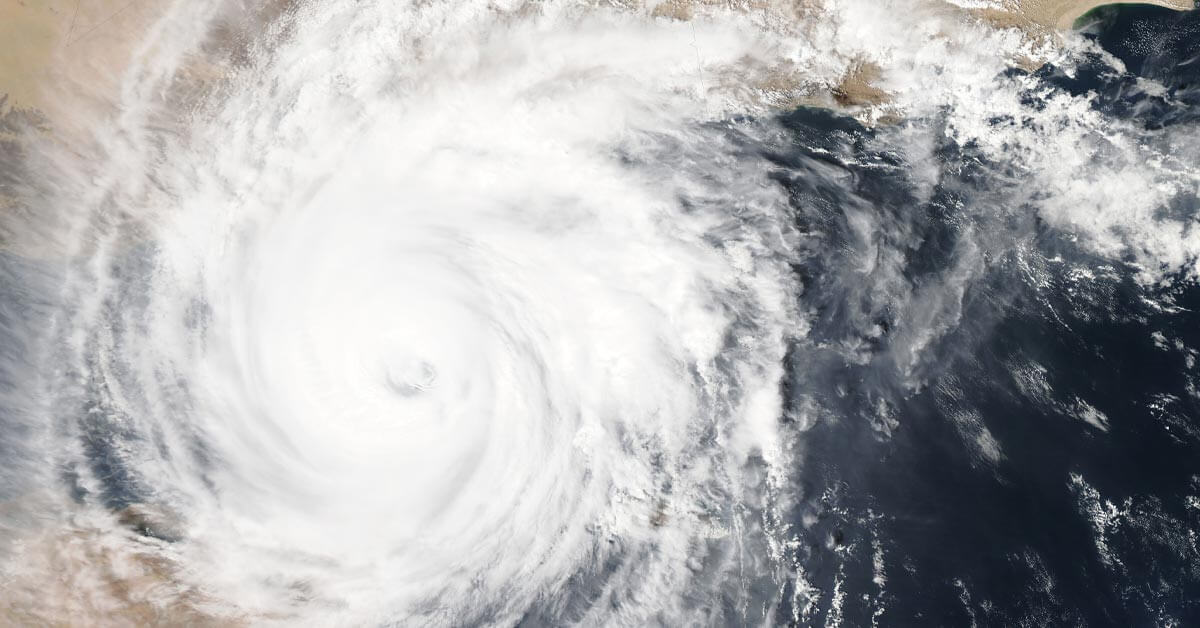
How to use virtualisation for disaster recovery
When we talk about disaster recovery plans, we tend to think of huge corporations with spare offices setup in different locations – desks, phones, PCs and servers just sitting there waiting for something catastrophic to happen to the old office*. When it does, the idea is that employees can simple switch to the spare office and continue working without missing … Read More
Which VPN Software Should You Choose?
In this blog Josh Peacock, one of the network engineers here at Optima will compare 3 of the most popular VPNs on the market today. IPVanish vs IPVanish vs NordVPN Firstly, what is a VPN? VPN stands for Virtual Private Network, it essentially adds you onto another Network and all your traffic goes through that Network. You can connect to … Read More
How to safely browse the internet
Now we use the internet to such an extent we need to make sure our details and browsing history is safe and secure. What are Cookies and what do they do? Cookies are used to track our browsing history and are used by companies to target advertising based of our searches. In some instances, this is useful as it shows … Read More
New Voluntary Code for Banks to Repay Victims of Push Payment Scam
There is finally some hope for the thousands that have fallen victim to so called ‘push payment’ scams with the announcment of a new voluntary code for Banks. Push Payment scams are where a fraudster seems to highjack emails and ask people to pay an outstanding bill or invoice to a different Bank Account. The account in question is owned … Read More
Check if any of your online ‘identities’ have been compromised with Hack Notice
Have you ever wondered if your gmail account has been hacked? Or your Amazon account details leaked somewhere on the dark web? A website called Hack Notice can help you find out. What is Hack Notice? Hack Notice is a website that allows you to enter in your “identities” to be monitored. These can be particular email addresses or freetext … Read More
New Scam Attempts to Blackmail People for ‘viewing Adult Content’
Scammers. The scourge of the internet! Always looking for new ways to make innocent people part with their hard-earned cash. A recent scam involves sending people an email claiming they visited adult websites. They pretend these websites downloaded malware that gave the scammer access to various aspects of the recipients computer. These include what they type and also access to … Read More
5 tips for keeping your network secure
Do you think your network is safe? It’s not just cyber criminals that can bring down your network and compromise data; careless users or disgruntled staff can be just as bad. Your network security is made up of hardware and software, policies and procedures which work to defend against threats to your systems. Layers of hardware and software can prevent … Read More
- Page 1 of 2
- 1
- 2